A lot of people don’t think their social media accounts are safe at all times. However, people continue to use them as a part of their daily routines and to connect with those around them.
With people connecting with others all the time, you might even ask yourself, “how can I track my boyfriend by phone number for free?” While this is common, people always do their best to protect their own social media accounts.
There are several ways through which you can use to safeguard your social media accounts. Fortunately, this guide looks at the best ways to achieve this goal.
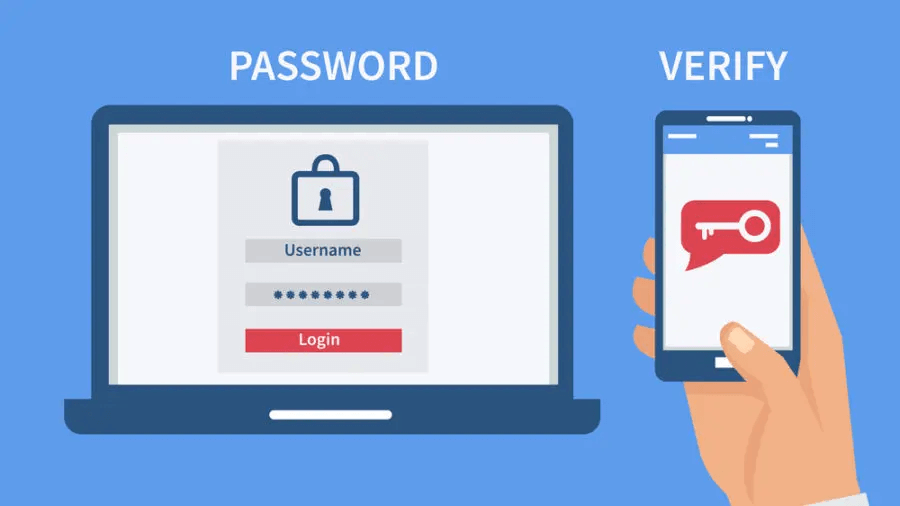
1. Always Enable Two-Factor Authentication
Two-factor authentication is one of the best ways for how to keep social media accounts safe. It also goes by the term 2FA and is imperative for optimal safety. The 2FA process involves using a two-step method to verify whether you are a legitimate social media account user.
Usually, the 2FA approach involves verification that is sent to your e-mail and personal phone number. You then have to input the codes on the corresponding social media pages to access the profiles.
The best part about using the 2FA approach is that it’s simple to use. You don’t need any technical skills or software installation procedures to start using the 2FA. Once you set up the 2FA, it will run for as long as any new user or device tries to access the account.
It’s an excellent technique that can deter any illegal access to your profile. With a single method of authentication, hackers might find it easy to hack your data.
2. Never Share Account Passwords With More People Than is Necessary
Social media passwords function in the same way as keys to the padlock of the door. It’s one of the best ways for how to avoid getting hacked on social media. While you can have several copies of the same key, it’s never a safe approach for many users. Further, a study has found that 95% of people share up to 6 passwords, making them easy targets for hackers.
This is because you will never have a method of tracking the specific individuals who access the account at a particular time. You should never share the password to your account with any other user.
However, in a business context, find accountable people who can access the password or social media account. Ensure you make them aware of the importance of using social media accounts ethically.
Awareness will be a powerful resource for you when sharing account passwords with many people. However, remember to set a limit for the number of users who can access the given system at any point.
3. Set Up Strong Passwords For All Accounts
Again, as we have previously mentioned, you have to find helpful ways of securing this information with passwords. The passwords are essential in ensuring no hackers can access your business’ social media accounts.
Hackers and malicious individuals today use sophisticated techniques to hack social media account profiles. The common ones they use include phishing, brute force attacks, and artificial intelligence.
While your business account might be prone to such attacks, a good password can help the success of such an issue. A good password has to possess specific characteristics, including:
- Should contain a unique character such as $ or &.
- It should not be a common phrase or word.
- Should contain upper case letters and numbers.
- It should be changed regularly.
4. Use a VPN When Accessing Your Account and Using Public WiFi Networks
Believe it or not, but a VPN is one of the best ways to prevent getting hacked. A VPN is software that masks your Internet Protocol (I.P) address.
Usually, VPNs contain specialized algorithms that bounce your traffic in between different services. For instance, if you are in Kyiv and you want to mask your location, the VPN will mask your I.P so that no user can trace your location.
Doing this helps reduce the likelihood of anyone accessing your personal information or directing attacks to your accounts. Below are some of the steps involved in using VPN:
- First, pick a reputable VPN service provider.
- Invest in a suitable service package.
- Install the VPN software on your device, and get the browser plugin.
- Start the software, or activate the plug-in. Some VPNs let you customize various other features.
- Then choose your preferred location, and activate the application.
- Next, search on Google using the term “what is my IP.”
- You should notice that your locations read differently.
5. Install Antivirus Software on Devices Used to Access These Accounts
Virus and malware are the leading internet security threats today. The average internet user doesn’t have the resources or skills to detect the presence of these threats. Here is where antivirus software is beneficial for how to stop a hacker.
Antivirus software helps to safeguard your system from any unusual software. It runs in the background, constantly looking out for system threats. Such security software also works well alongside solutions such as firewalls.
Before installing antivirus software, ensure you choose one from a reputable brand. Plus, the best antivirus software is always available on a subscription-based service. While it’s a solution at a cost, it’s still a powerful and convenient way to protect your business.
The software might also require regular updates because computer security threats evolve rapidly. A good example you can consider is Norton.
6. Check Your Mailbox to Spot Suspicious Login Attempts
You have to be as sharp as a hawk when it comes to detecting any compromise that might exist to your social media accounts. One of the best ways to be aware of social media account compromises would be to detect any suspicious login attempts.
Usually, social media platforms keep a record of when someone attempts to access your account. It usually comes as a notification of the 2FA code or a message from the given social media platform.
You have to check the mailbox of the associated account regularly. Doing this ensures you can detect any account compromises ahead of time.
Conclusion
As you have seen, social media accounts are prone to illegal access, which can harm your business. Creating a good reputation sometimes takes lots of resources, which can disappear in a single day, thanks to illegal access.
However, you can stop such issues by staying informed and alert for such threats and by following the precautions mentioned in this guide.